Best Laptop For Hacking 2025 – Guide & Tips

The tiniest computer. Mostly used for programming testing/practice in engineering but very popular among hackers.
The point is…it doesn’t matter what computer or laptop you use.
However…
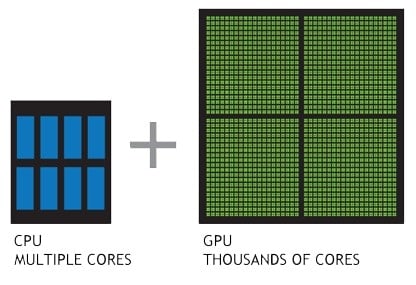
That doesn’t mean good hardware is useless—it definitely helps! For instance, some scripts will run faster with a dedicated GPU that has many cores, potentially reducing the time to crack a password from weeks to minutes.
Before we continue, let me clarify:
Use this information only for hacking into systems you have permission to access. This is called “ethical hacking.” With this knowledge, you could pursue a career in cybersecurity or as a penetration tester, helping to defend against criminal hackers (and earning impressive salaries in 2024, by the way).
Best Laptop Specs for Hacking
Before diving into the hardware, let’s go over the main ‘apps’ and ‘tasks’ that a hacker or pen-tester typically uses. This should clarify why certain hardware specs are more favorable than others. I’ll keep it brief here, but check the last section for detailed tips and links.
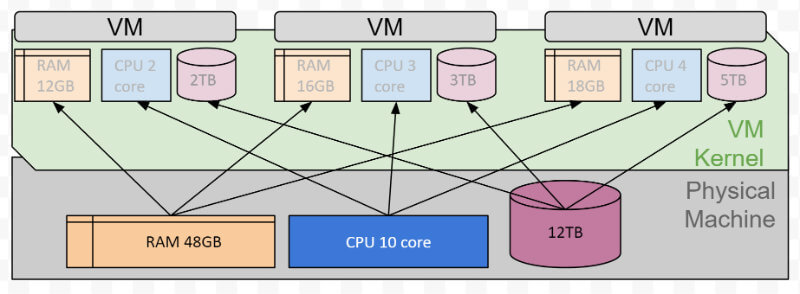
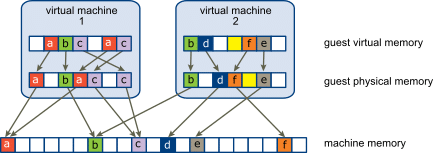
1. Virtual Machines: Hackers typically use a setup with Windows + Kali Linux. Running a single VM doesn’t require much RAM or CPU power. However, if you plan to run nested networks (VMs within VMs) or several VMs simultaneously for simulation purposes, you’ll need substantial RAM and multiple CPU cores
2. Programming Languages: This doesn’t require good hardware but SSD+extra RAM is very handy. Also, it’s always better to pick a machine that can FULLY support Linux.
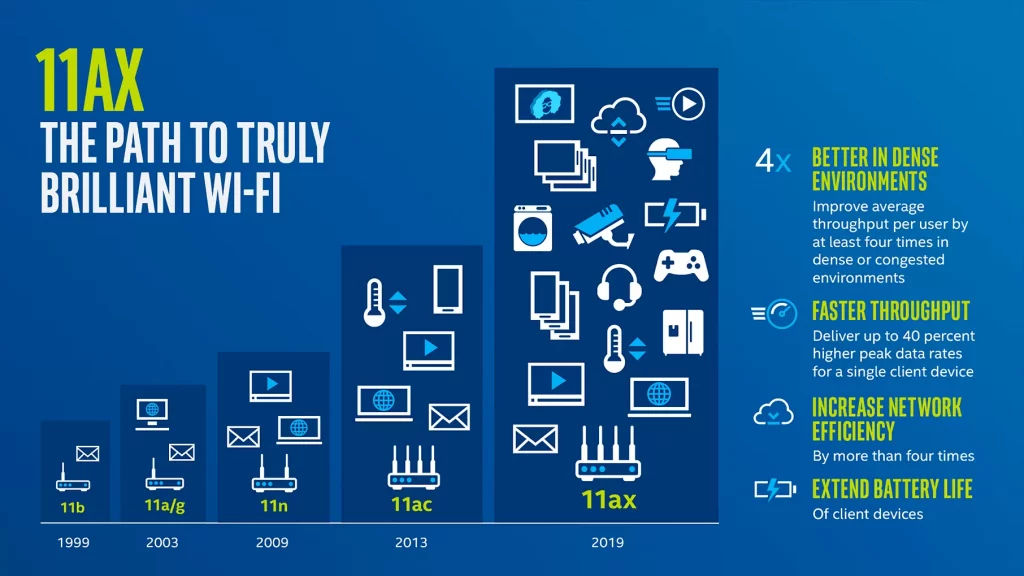
WiFi 6 or latest: will have compatibility with the most recent WiFi Protocols plus backward compatibility with the older protocols , super useful to target different networks like your neighbor’s WEP secured network *cough* I mean to test his network for vulnerabilities with his consent.
Using a mouse gives you more speed for tracking bugs and interacting with the OS (yours or your target) . Trackpads are too slow.
Storage(Optional)
Even if you’re saving tons of hacker software and scripts, 128GB will last you a lifetime.
Make sure your storage is either an SSD or one of its fast variants (eMMC, Flash), as this will make virtual machines responsive and won’t keep you waiting (unlike traditional spinning hard drives) to run your hacking scripts and complete your tasks.
These laptops aren’t anything out of the ordinary—you could find similar ones at your local computer store.
Heads up: Linux doesn’t come pre-installed, so you’ll need to set that up yourself.
What’s the deal with these laptops, then?
They’re just solid options for people in the US, with good build quality and cooling systems that’ll help them last longer than average. All of them have the specs needed to handle the programming languages and tools hackers use, plus they can run multiple virtual machines so you can set up simulated networks and practice.
Laptop #5: This one’s kind of overkill for basic hacking. It’s a gaming laptop, which means it can handle heavy-duty tasks like password-cracking scripts and, of course, AAA games (you could even mess around with some cheat scripts). It’s pricey, though, so think of it as more of an FYI than a must-have.
I’ll keep diving into how each laptop stacks up for hacking as we go along
1. Acer Aspire 5 14 Slim
Cheap Laptop For Hacking
Core i5-1335U
8GB LPDDR5
Intel Xe Graphics
512GB SSD
14” Full HD IPS
3.75 lbs
3 hours
WiFi 6E
| Acer Aspire 5 14 Slim | |
| PROS | CONS |
|
|
2. Lenovo Ideapad Business
Budget Laptop For Hacking
 AMD Ryzen 3 7320U
AMD Ryzen 3 7320U
8GB DDR5
AMD Radeon 610M
256GB SSD
15” full HD IPS
3.48 lbs
8 hours
WiFi 6
Fingerprint Scanner
Windows 11 Home
| Lenovo Ideapad Business | |
| PROS | CONS |
|
|
3. Lenovo ThinkPad T16
Best Lenovo Laptop For Hacking
Intel Core i7-1355U
32GB RAM DDR5 (Upgradeable to 48GB)
Intel Iris Xe Graphics
1TB PCIe NVMe M.2 SSD
16” FHD IPS 300 nits
3.7 lbs
10 hours
Windows 11 Pro
WiFi 6
| Lenovo Thinkpad T16 | |
| PROS | CONS |
|
|
4. Lenovo ThinkPad E16
Best Laptop For Hacking
AMD Ryzen 5 7530U
24GB RAM
AMD Radeon 610M
1TB PCIe NVMe SSD
mdi-icon name=”monitor” size=”2x” color=”black”] 15.6″ 1920×1200 (WUXGA)
4.34lbs
10 hours
Wifi 6 802.11AX
| Lenovo Thinkpad E16 | |
| PROS | CONS |
|
|
5. MSI Raider 18 HX
Best Laptop For 3D Animation – 4090RTX

Core i9-14900HX
64GB DDR5
NVIDIA RTX 4090 16GB vRAM
2TB NVMe SSD
18” 120Hz UHD+
7.9 lbs
1 hour
4090RTX GPU: 9728 CUDA Cores
So, if you’re serious about running password-cracking scripts or doing wireless network testing, the 4090RTX is basically the holy grail. It’s got close to 10,000 CUDA cores, which is massive. Those cores are gold for anything that involves parallel processing, like password cracking, data science, or machine learning.
Yeah, this laptop also has a 14th-gen Core i9 CPU with 24 cores, but honestly, that’s not the big deal here for these tasks. The GPU is where the magic happens because GPU cores are built for this kind of workload. To put it in perspective: a GPU with 10,000 cores versus a CPU with 24 cores? The GPU’s going to be miles faster when it comes to cracking WPA and WPA2 networks. You’re looking at something like 400 times the processing power for stuff that relies on CUDA cores.
Testing Labs
This setup is also perfect if you’re planning to mess around with virtual labs for pen-testing. VMs lean heavily on CPU cores, so this Core i9 does help here. With 32 threads, you could technically run up to 60 virtual machines at once (assuming you’re doubling up VMs per thread and leaving a couple for the host OS). It’s like having a mini lab in one machine, which is awesome if you’re trying to simulate complex network environments.
Bottom line: this rig isn’t just overkill—it’s overkill in all the right ways. You get the muscle for both GPU-heavy tasks like password cracking and CPU-heavy tasks like running loads of VMs for pen-testing.
| MSI Raider 18 HX 18 | |
| PROS | CONS |
|
|
Warning: Read Before Checking Next Section
So please get nto ethical hacking instead. You’ll learn all the tricks and schemes hackers use and still be able to get a high paying job through penn testing or security.
Hacking: Software & Hardware Guide
The information presented here is from those years attending hacking conferences and hacking thereafter as a hobby.
These conferences were ethical hacking talks. Hackers do not gather and promote hackery at public conferences. That would get everyone under investigation.
I assume most people reading this barely know how to write a piece of code so to make it much easier I’ll divide this section in three parts:
- Types of hackers
- Software for hackers
- Hardware for hacking”
1. Types of Hackers
True hackers have a deep understanding of how computer networks function:
What’s a stack? A heap? How do architectures and assemblers work? What about network protocols—their strengths and weaknesses?
With this knowledge, a hacker can quickly spot vulnerabilities in a network and know how to exploit them.
Experienced hackers don’t rely on fancy software for this.
They can analyze and understand network traffic just by looking at the code. That’s right, with just a glance at the code, they can interpret how network traffic flows and how applications operate, as shown below:

- No Need for Supercomputers:
You don’t need a high-end machine just to look at code. A basic laptop with 8GB of RAM will do the job for writing, editing, and viewing code. That’s why I emphasize learning coding fundamentals over searching for downloadable “hacking” software online. - Linux: A Must for Hackers
Even that old laptop gathering dust in your grandma’s basement can turn into a powerful tool if you install Linux. Here’s why Linux is essential:- Lightweight OS: Some Linux distributions (or “distros”) are so lightweight they can run smoothly on old, budget hardware.
- Purpose-Built Distros: Distros are essentially different Linux versions tailored for specific needs, from general usage to ethical hacking.
- Native Programming Tools: Linux is popular because it comes pre-installed with many programming languages and has a vast library of resources and packages specifically for developers.
- Terminal Mastery: The Linux terminal is a must. You’ll need to get comfortable with it from day one, though it might take a few weeks to feel proficient.
- Hardware and Network Control: Linux provides complete control over hardware and network ports, unlike Windows or macOS. With Linux, you can manage your hardware and network configurations down to a fine level of detail.
- Enhanced Security: If you know what you’re doing with ports and network management, you can make your Linux system much harder to hack.
Now we’ll go over the three types of hackers!
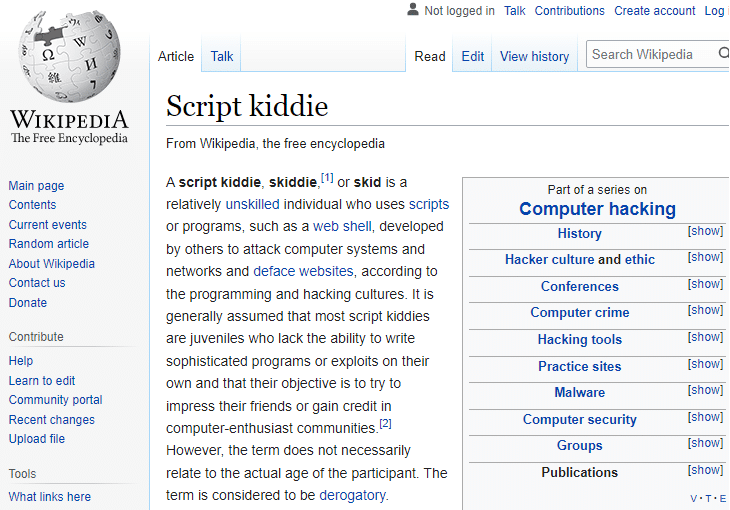
SCRIPT KIDDIE
Advanced Programmer (Almost Hacker)

If you’re a computer engineer, you already have a head start in the skills required for hacking.
In fact, many hackers come from a background in computer science or engineering. They often start by exploring operating systems and networking, learning how these systems communicate and where vulnerabilities can emerge. From there, some advance to creating custom scripts and tools for security testing, which involves ethical hacking practices.
After becoming comfortable with fundamental hacking frameworks, like Metasploit, they may begin creating customized modules or scripts for specific security needs. This kind of development is advanced and often pursued by security researchers or experienced exploit developers, not by those new to the field.
Eventually, they might start exploring exploit development. This can include learning how to create simple worms, browser exploits, and other test scripts. Writing these requires solid knowledge in programming languages, security concepts, and, ideally, a well-controlled testing environment.
For such development work, a machine with at least 8GB of RAM can handle basic coding and virtual machines. However, if they’re testing across several virtual environments, like simulating various OS setups, 16GB of RAM is preferable to keep everything running smoothly.
To safely test their code, ethical hackers often set up isolated virtual labs, sometimes with multiple VMs simulating different target systems. Running these in isolation is crucial to prevent unintended exposure to any external networks, which would cross into unethical territory. When the testing is complete, professionals in ethical hacking or cybersecurity stay within legal boundaries to avoid crossing into malicious activities.
It’s important to note that professional ethical hackers stop their work at testing within isolated, controlled environments—crossing into live, unauthorized testing would be illegal.
Stealthy Real Rogue Hacker

2. Software
Operating System: Not Windows!
During the first hacking conference I attended. There was a problem with the projector and the presenter asked the audience if anyone had a Windows laptop he could borrow to run the presentation.
There was no one in that huge crowed running anything but Mac OSX or a Linux Distro.
Many people started commenting on how innappropiate was for someone like him (supposedly an ex-hacker) to ask such question. One person even stood up and called him out saying he was obviously spending way too much time with the layman and business people rather than penn-testers or hackers.
He then proceded to clarify that he had Mac OSX, Linux OSX and Windows 7 rigs back home but he decided to bring this time his two-goody shoes Windows laptop to the conference for obvious reasons.
Everyone laughed!
Why Linux?
It basically comes down to being a very flexible operating system.
In other words, you can do whatever you want with it and the fact that it’s open source means you can tailor the Operating System to look and operate as you’d like.
Like OSX (mac) , it’s also a hybrid OS, which basically means it has both a command line interface (terminal) and a graphical user interface for you run code.
You can use either to fully operate the system to your liking. It also gives you full control of all the hardware in your computer.
Now hackers will usually make their own Linux Distro (anonymous) but you don’t need to do this . There are HUNDERDS of readily to install Linux Distros with hacking and penn testing in mind. They even have preinstalled software and languages for these purposes.
Here’s a run down of the most popular “hacking” Linux Distros:
The most popular distro for pen-testing. Developed by Offensive Security as a re-write of BackTrack many many many years ago and it still tops the list of all operating systems used for (ethical) hacking.
Not the best distro if you’re a newbie.
The community is filled with advanced hackers so you’ll be vulnerable to attacks. Unless you know what you’re doing and know your way in and out of the OS, it will backfire on you eventually and even attack vector will succesfully hack your system.
Someone who knows how to use Kali Linux will easily hack someone who only has a few months using it.
Tails
For illegal tools like NMAP , most hackers install a Distro like Tails. This is because Tails has best degree of anonymity super important when going in Live Mode.
Cybor Hawk
This is a great alternative to Kali Linux. It’s mainly used for penn testing . Unlike Kali, it has an amazing GUI which makes configuring any rig much much easier. Highly recommended for newbies.
This is a Debian-based distro developed by Frozen Box’s team. It’s popular for pen testing, computer forensics, cryptography. In other words, ethical hacking.
BackBox is an Ubuntu-based Linux Distro mainly used for security assessment and penn testing.
A live Linux environment pre-configured for penn testing work especially web based penn testing.
Other popular distros with very strong points in their own right are:
- Pentoo Linux
- DEFT Linux
- Caine Linux
What about the software specifically designed for hacking facebook accounts, cracking WEP Wifi Passwords and so on?
I can’t link to any malicious software here because that would get me into trouble.
However, with a bit of searching, you can find plenty online.
For study purposes, think of these as scripts rather than software. Essentially, they’re just lines of code outlining a sequence of steps to activate or control various computer processes to hack a target. Download them, open the files in an IDE or notepad, and try to understand the code. Keep revisiting them as you learn more about programming and hacking.
They’re commonly referred to as:
- Virus/worms. Do not click the link unless you have an antivirus.
- Browser Exploits: Don’t click the link unless you want your entire browsing history published on facebook/reddit. Jk.
- Email client buffer exploits: Don’t click here if you want everything on your email exposed to the web. :’)
3. Hardware for Hacking
Again if you are a newbie just get started with whatever you can get right now even if its a laptop you already have. Even an old cheap laptop with the screen falling off is a good start, once you install Linux on it, it wil lfly and you’ll be able to learn all the basics. for hacking
A) CPU
16GB RAM and More: Only for Pen-Testing
If you really want to learn all there is to know about ethical hacking and what hackers do, you will need to buy an external wifi receiver (or adapter) that can support packet injection (this is a big part of hacking).
You’re going to use this to run code which will use this adapter to “attack” other WiFi networks.
Dual band or tri band AC network cards (like the latest WiFi AX or the latest WiFi 7) are the best for getting into WEP secured networks quickly but you’re not going to find WEP networks these days. Even your neighbors will use a WiFi network with WPA2 encryption. So nothing is going to be cracked quickly.
Design
Hackers buy something that’s very portable and easy to destroy. They like laptops that can support an additional hard drive and make it easy to remove (to be destroyed later for evidence purposes).
They will NOT install anything on the M.2 Drive (built-in) which is attached to the motherboard for obvious reasons.
They will also switch from one MAC address to another (super easy if you have more than one network connection).
Desktop + Laptop
The vast majority of hackers get a cheap 300 dollar laptop with a lot of battery life like a refurbished MacBook. In fact, the MacBook was the most popular laptop on every convention I have attended, nearly 75% of the auditorium had a MacBook, the other 25% either had a Dell/Lenovo ThinkPad.
Why?
Because they can just SSH into their more powerful rigs back home to access virtual machines and have access to different operating systems
Their desktop rigs are equipped with top of the line GPU and CPUs to do all the cracking/run injection packets and every other type of attack that requires a lot of processing power.
They use their cheap 300$ MacBook to simply write all the scripts/code they will run back home.
It doesn’t necessarily have to be a MacBook….
All you need is a Core i3, a recent integrated GPU and the rest can be spent on extra RAM (this is the cheapest hardware to upgrade – 15$ bucks will get you an extra 4GB RAM).
Then they install a Distro like Kali Linux (or any of the other distros mentioned before , they will all have more or less the same pre-installed software you will use).
Now that’s for ETHICAL HACKERS or those learning how to become a hacker.
Criminals hackers use whatever device they can get their hands on because they have to trash it later for evidence purposes.
Some even go as far as building their own. They design them with enough hardware to do all the stuff they have in mind and make it cheap enough at the same time so that they can be destroyed later for evidence purposes.
Last Comments
For more specialized tasks, you will find yourself looking at FPGA boards or software defined radios, but don’t worry about those things until you deep dive into this field after a year or two.
Anyways, this info is all over the web, not necessarily on the first page of the search engines but it’s still there (you may have to go through the last pages of google).
If you need more info, just look up “Ethical Hacking”.
Even udemy will have a lot of free courses about it.
What you’ll find on youtube though are usually lectures given by guys who got caught and eventually went to jail but worked out a plea deal with the Feds (kind of like the movie “Catch me if you can” ), so they’re definitely teaching all the good stuff.
The same goes to you : unless you’re really good, or really lucky, you will eventually get caught. Study hacking for penn testing purposes instead, lots of money and you can call yourself a hacker too!
Author Profile
- I am physicist and electrical engineer. My knowledge in computer software and hardware stems for my years spent doing research in optics and photonics devices and running simulations through various programming languages. My goal was to work for the quantum computing research team at IBM but Im now working with Astrophysical Simulations through Python. Most of the science related posts are written by me, the rest have different authors but I edited the final versions to fit the site's format.
Latest entries
 wowDecember 18, 20255 Best Laptops For World of Warcraft – Midnight & Classic (2026)
wowDecember 18, 20255 Best Laptops For World of Warcraft – Midnight & Classic (2026) LaptopsDecember 17, 2025The 4 Best Laptops For Virtualization of 2026 (10-50 VMs ATSM)
LaptopsDecember 17, 2025The 4 Best Laptops For Virtualization of 2026 (10-50 VMs ATSM)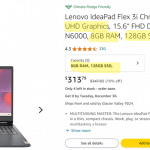 Hardware GuideDecember 17, 20252026 Beginner Guide to Reading Computer (Laptop) Specifications
Hardware GuideDecember 17, 20252026 Beginner Guide to Reading Computer (Laptop) Specifications LaptopsJune 30, 2025Best Laptops for Computer Science (July 2025 )
LaptopsJune 30, 2025Best Laptops for Computer Science (July 2025 )




Hey it’s me Ronald from Zimbabwe. Is was so amazing. Thank you for advise, but i am inspired and motivated by programming and hacking and i sometimes learn on my own. I don’t know if you could help me because being alone in studying computers is to hard for me. My aim was to study cyber security. Will you help me???